Recognize phishing attacks and stop them in minutes, not days
In your demo, you’ll learn:
- How to detect threats in real-time
- How to condition employees against real threats
- How to analyze and respond to email threats
- How to stop phishing attacks in their tracks
LAST 90 DAYS: Cofense has found 13,000+ malicious emails in environments protected by Proofpoint
How Our Phishing Prevention Works
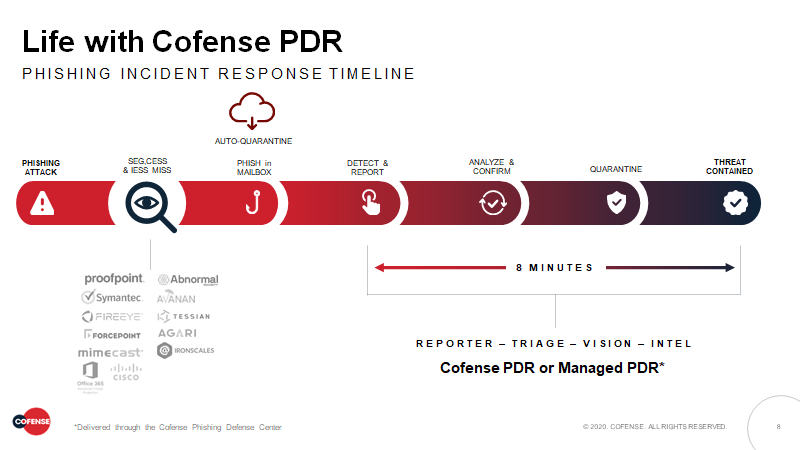
Cofense helps global organizations quickly detect and respond to phishing attacks that evade perimeter controls.
Built on the world’s largest data lake of phishing threats found by real people, Cofense combines the power of human detection with an automated response, enabling your teams to stop phishing attacks in minutes.
It’s advanced phishing prevention technology augmented with collective human intelligence – the first solution purpose-built to quickly detect and stop phish that reaches the inbox.
What Sets Cofense’s Phishing Defense Apart…
Network Effect
Remediate faster with insights from the largest network of human sensors.Automated Response
Accelerate response and quarantine every email in a campaign.Unbiased Intelligence
Understand phishing threats while fine-tuning perimeter controls.Focused Innovation
Dedicated to staying ahead of the #1 cause of breaches – phishing.Remote Work Phishing Threats Experiencing Exponential Growth
With so many people working from home, remote work software like Skype, Slack, Zoom, and WebEx are starting to become popular themes of phishing lures. Cofense recently uncovered an interesting Skype phishing email that an end user reported to the PDC.
Although there are many ways to exploit a compromised account, threat actors often choose to send out phishing campaigns masquerading as a trusted colleague or friend. It is not uncommon to receive emails about pending notifications for various services. Threat actors anticipate users will recognize this as just that, so they take action to view the notifications.
See how we train employees working from home on the dangers of phishing, keep email gateways secure, and protect businesses from remote phishing threats.
We're Trusted By The Names You Trust
Working With Cofense Has Been A Very Easy Thing To Do
“Working with Cofense has been a very easy thing to do. The support that we got from them during our ramp up phase was excellent and all the staff I have spoken to have been knowledgeable and able to help or was honest enough to say they didn't but knew who to call to help. ...”
Role: Security and Risk ManagementFirm size: 3B – 10B USD




